Verify every device,
secure any user.
Privacy-respecting Zero Trust alternative to traditional MDM for securing BYOD, freelancer, contractor, personal, and unmanaged devices.Securing devices for leading organizations like
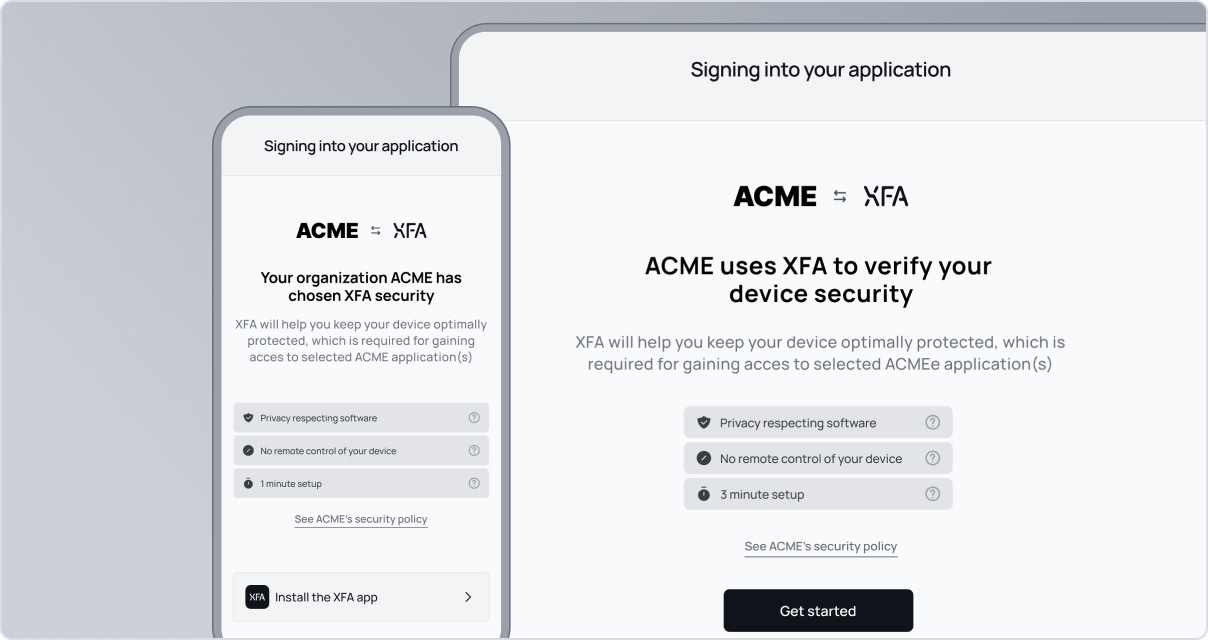
Privacy-first device security. XFA secures BYOD, managed, and external devices with a lightweight security layer without intrusive device management.
MDM alternative for hybrid environments. Let people work on any device they want with a smooth experience that boosts productivity, happiness and offers security.
Learn how to protect BYOD & Freelance devicesXFA has an user-friendly and straightforward process for onboarding people. Additionally, I value that it supports a bring-your-own-device policy, unlike many other tools out there, which are both costly and restrictive.

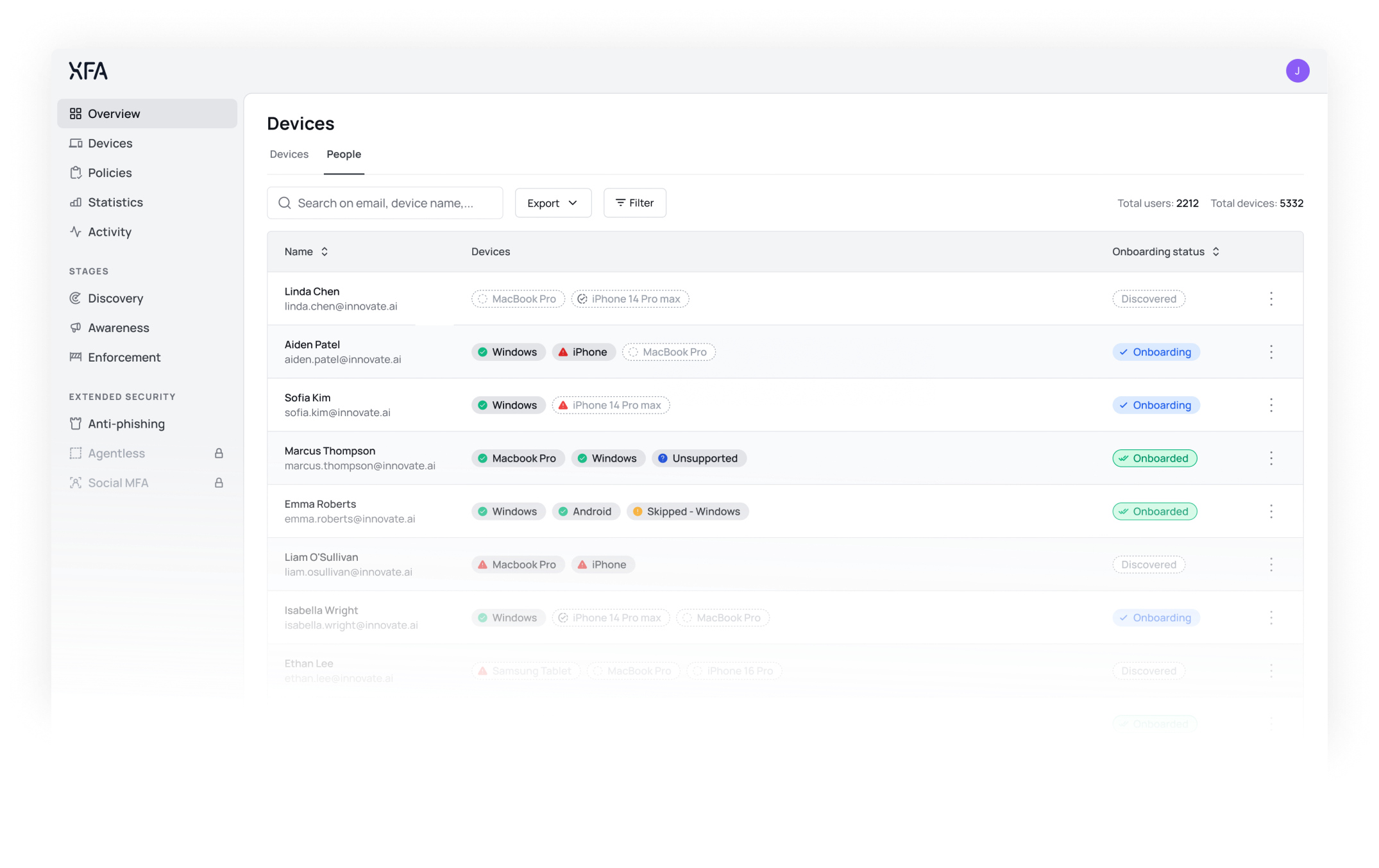
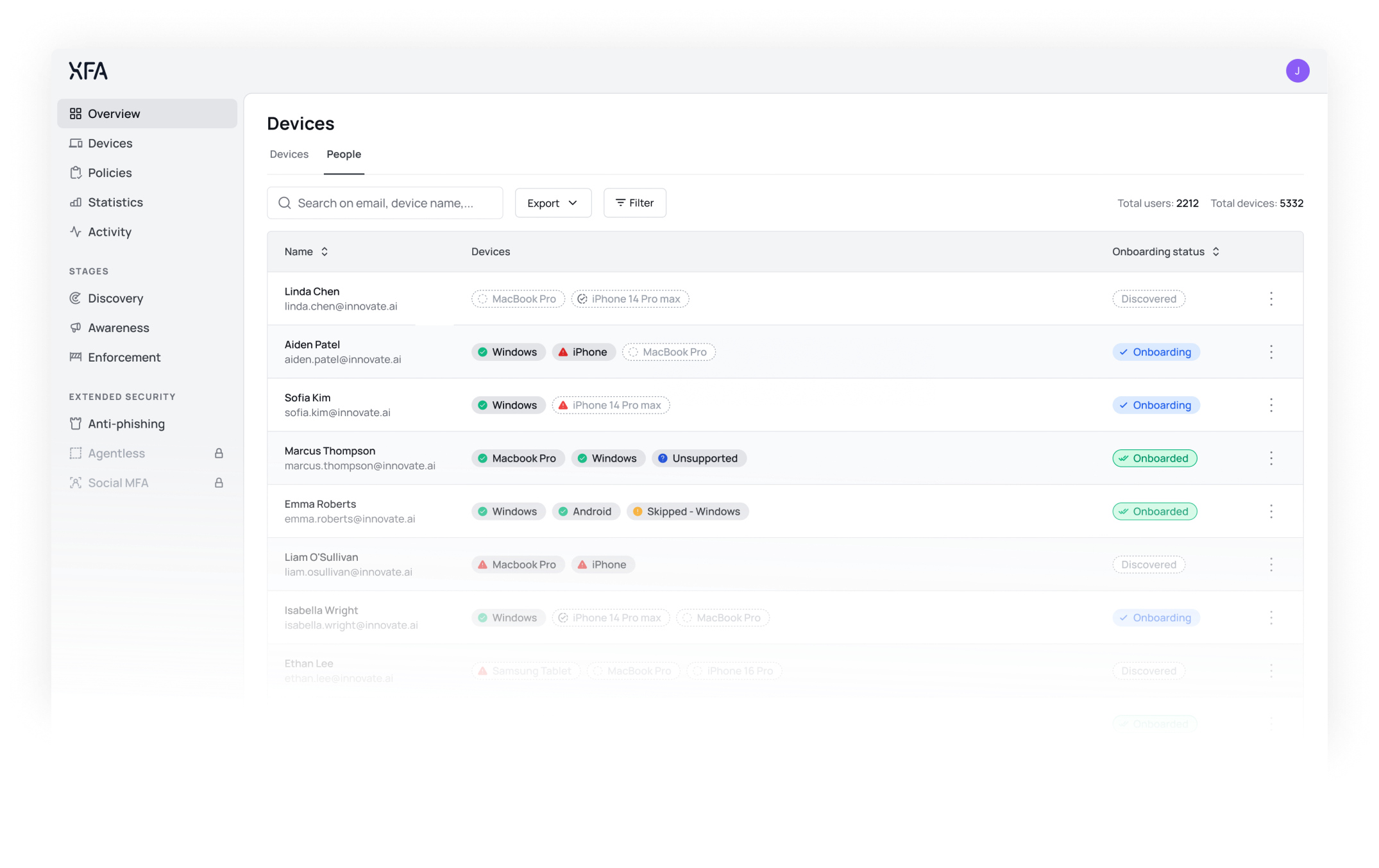
Discover all devices.
Raise security awareness.
Enforce protection.
Device Trust in minutes.
We integrate with your Identity Provider, discover all connected devices, check their security, and enforce compliance-ready access controls.
Discover every device used for work. Zero Trust device access without an MDM. XFA gives the visibility you need without taking over devices.
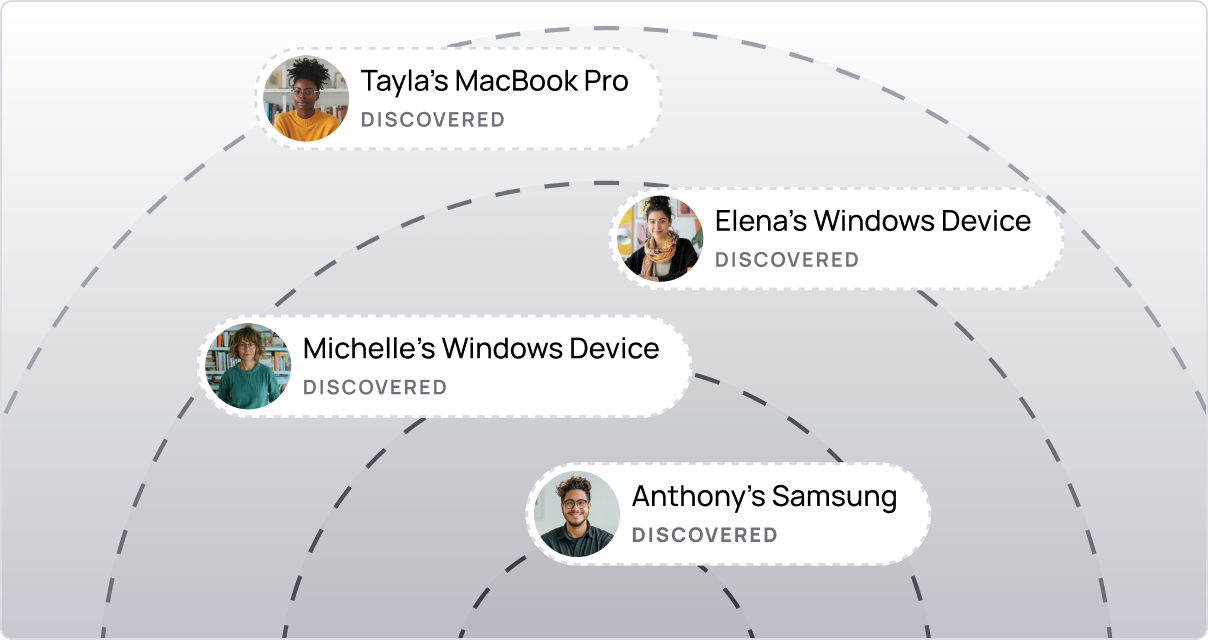
DISCOVERY
Discover every device accessing your platforms. In just minutes
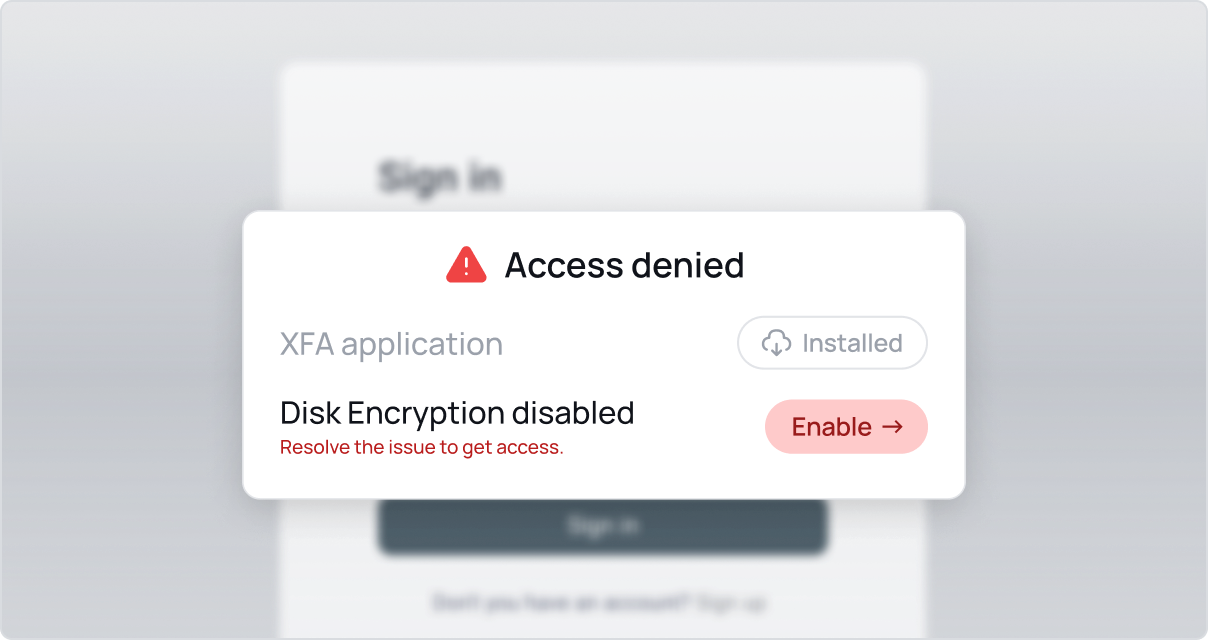
ZERO TRUST
Only allow secure devices to access your business data
Achieve compliance certifications with ease. Secure all devices from BYOD to fully managed, get complete visibility and the evidence you need for compliance certifications.
COMPLIANCE CERTIFICATIONS
Get device security evidence for certifications like ISO 27001, SOC2, Cyber Essentials, NIS2, and more
GRC PLATFORM INTEGRATIONS
Share your compliance status with platforms such as Vanta, Drata, Trustcloud and Thoropass.
Discover every device used for work. Zero Trust device access without an MDM. XFA gives the visibility you need without taking over devices.
USECASES FOR INDUSTRIES
Whether you're in healthcare, tech, or education, every sector needs device-level security it can trust.
SCALABILITY
Quick and easy self-onboarding for your entire team with confidence
What our customers say
"XFA is crucial for us, as we rely on both managed and unmanaged devices. XFA's discovery phase helps us identify what devices are accessing sensitive information and ensures they comply with our security policies."
Read the full testimonial →No time for a meeting?
Watch our solution video now.

We'd love to show you our solution and how:
- Every device is discovered automatically.
- Security is enforced without taking control or ownership of the device.
- Users can verify their devices from anywhere, in seconds.